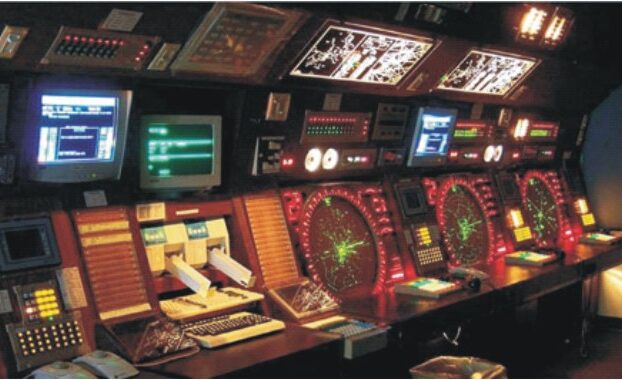
C4I
Spectrum of Signals
Spectrum of signals Over the years as its satellite launch facilities grew and matured India has been toying with improvements to the Global Positioning System of the US and the Russian Global Navigation Satellite System (GLONASS) with the intention of creating its own Indian Regional Navigational Satellite System (IRNSS) consisting of seven satellites and a […]
Satellite
Avenues in Space
Avenues in space The smooth launch of India’s home-grown 1858-kg radar imaging satellite RISAT-1 by means of XL version of the four stage Polar Satellite Launch Vehicle (PSLV) on April 26 from Satish Dhawan Space Centre (SDSC), the Indian spaceport in Sriharikota Island on India’s eastern coast, is considered a major boost to India’s defence […]
Aerospace Command
Mars Mission Success
India has created a splendid space history with the Indian Space Research Organisation (ISRO) successfully inserting the Rs 4500-million Indian Mars Orbiter spacecraft into its final orbit around the Red Planet on the morning of September 24th, 2014. It was indeed a space dream come true for India. With this spectacular achievement, India pulled off […]